IoT Hacking - Netgear AC1750 NightHawk - Firmware Extraction via Root Shell
Matt Brown
@mattbrwnAbout
I’m Matt Brown, an IoT security researcher and pentester with over a decade of professional experience. On this channel, I share my passion for hardware hacking, IoT pentesting and reverse engineering. Want hands-on IoT security training? Visit https://training.brownfinesecurity.com Need IoT pentesting services? Visit https://brownfinesecurity.com. Matt Brown: Christian, Husband, Father, and IoT security professional - Soli Deo Gloria
Video Description
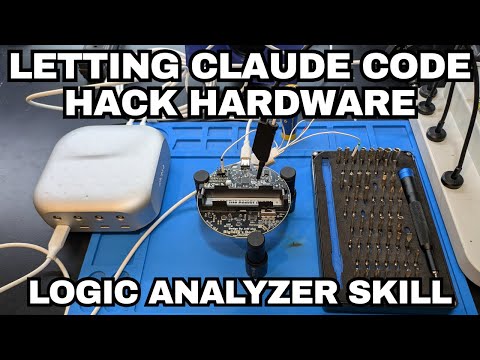
In this video we use the UART root shell discovered in the last video to show two common methods for extracting device firmware using shell access. IoT Hackers Hangout Community Discord Invite: https://discord.com/invite/vgAcxYdJ7A 🛠️ Stuff I Use 🛠️ 🪛 Tools: XGecu Universal Programmer: https://amzn.to/4dIhNWy Multimeter: https://amzn.to/4b9cUUG Power Supply: https://amzn.to/3QBNSpb Oscilloscope: https://amzn.to/3UzoAZM Logic Analyzer: https://amzn.to/4a9IfFu USB UART Adapter: https://amzn.to/4dSbmjB iFixit Toolkit: https://amzn.to/44tTjMB 🫠 Soldering & Hot Air Rework Tools: Soldering Station: https://amzn.to/4dygJEv Microsoldering Pencil: https://amzn.to/4dxPHwY Microsoldering Tips: https://amzn.to/3QyKhrT Rework Station: https://amzn.to/3JOPV5x Air Extraction: https://amzn.to/3QB28yx 🔬 Microscope Setup: Microscope: https://amzn.to/4abMMao Microscope 0.7X Lens: https://amzn.to/3wrV1S8 Microscope LED Ring Light: https://amzn.to/4btqiTm Microscope Camera: https://amzn.to/3QXSXsb About Me: My name is Matt Brown and I'm an Hardware Security Researcher and Bug Bounty Hunter. This channel is a place where I share my knowledge and experience finding vulnerabilities in IoT systems. - Soli Deo Gloria 💻 Social: twitter: https://twitter.com/nmatt0 linkedin: https://www.linkedin.com/in/mattbrwn/ github: https://github.com/nmatt0/ #hacking #iot #cybersecurity #reverseengineering #firmware
Dollar Store Must-Haves
AI-recommended products based on this video

GUUZOGG Tralalero Tralala Plush Toy, 15 Inch Italian Brainrot Stuffed Animal, Soft Shark Plushies Figure Doll for Adult Kids Boys Girls