Reverse Engineering Windows EXE files on Linux
Tsoding Daily
@tsodingdailyAbout
"Daily" Development Log of Tsoding. If you want to repost a clip from this channel, feel free to do so, but please credit the channel and provide the link to the original video. Thank you!
Latest Posts
Video Description
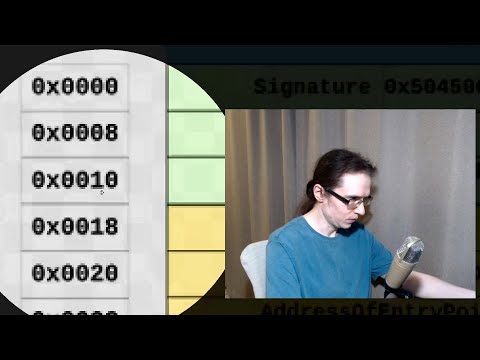
Streamed Live on Twitch: https://twitch.tv/tsoding Enable Subtitles for Twitch Chat Chapters: - 00:00:00 - Beatbox - 00:00:27 - Intro - 00:06:25 - Project Building - 00:15:43 - Loading EXE file - 00:18:08 - DOS Header and DOS STUB - 00:44:52 - COFF Header - 00:57:30 - Skipping Optional PE Header - 01:05:04 - Section Table - 01:28:36 - Dumping Raw Data of Sections - 01:32:16 - Trying to find CLR - 02:08:22 - CLI Header - 02:30:29 - Not Skipping Optional PE Header - 02:40:47 - Relative Virtual Address (RVA) - 03:24:43 - CLI MetaData - 03:36:10 - Stream Headers - 03:55:07 - CLI Streams - 04:05:32 - Outro References: - https://en.wikipedia.org/wiki/Portable_Executable - https://learn.microsoft.com/en-us/windows/win32/debug/pe-format - https://www.red-gate.com/simple-talk/blogs/anatomy-of-a-net-assembly-pe-headers/ - https://www.ecma-international.org/wp-content/uploads/ECMA-335_6th_edition_june_2012.pdf Topic: Reverse engineering an EXE file generated by the Mono C# Compiler to see if I can recreate it myself from scratch as part of the CLR target for the B compiler. Twitch Chat in Subtitles generated by: https://github.com/kam1k4dze/subchat Support: - https://github.com/tsoding/donate#support-tsoding
You May Also Like
Essential Linux Reverse Engineering Tools
AI-recommended products based on this video

TP-Link USB WiFi Adapter for PC(TL-WN725N), N150 Wireless Network Adapter for Desktop - Nano Size WiFi Dongle for Windows 11/10/7/8/8.1/XP/ Mac OS 10.9-10.15 Linux Kernel 2.6.18-4.4.3, 2.4GHz Only

Canoly Cold Press Juicer, 350W Slow Juicer Machine with 4.5" Wide Feed Chute, Masticating Juicer Supports Whole Fruits & Vegetables, Reverse Function, Easy to Clean with Brush, Space Black

iSpring RCC7, NSF Certified, High Capacity Under Sink 5-Stage Reverse Osmosis Water Filter, RO Drinking System, 75 GPD, Brushed Nickel Faucet, Patented Top-Mounted Faucet Design for Easy Installation

Reverse Osmosis Water Filter Countertop, 5 Stage Ro Water Filtration System with Remineralization Glass Pitcher, 4:1 Pure to Drain, TDS Real-Time Displaying, 4L Capacity Tank for Home Office